Wow, what a year. One thing’s for certain, 2020 is one year that will never be forgotten. Covid, Lockdown, Furlough, words that have been added to the canon of speech this year. And, to cap it all, Christmas is just around the corner and the world is still full of massive levels of uncertainty.
Whether you are working from home, #WFH, working in an office or still out and about I know that as Christmas approaches the big wind-down starts to feature in our minds.
Nothing wrong with looking forwards to Christmas but it’s important that you don’t allow your Cyber Security guard to fall too.
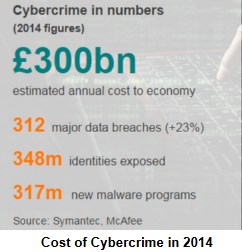
Why not? Simply because the hackers and cyber criminals won’t – if anything they’ll be upping their activity because they know that our minds will be on other things. In previous years we’d have been looking forward to Christmas Markets, Christmas parties, gifts, food, television and everything else that’s associated with the season of goodwill.
Our vigilance MUST remain high, both in the office and when working from home. Keep your eyes open for suspicious looking emails, especially those coming from unexpected quarters, with messages that promise much, such as tax refunds or deliveries of items you don’t remember ordering. Also beware of emails with links to websites that look OK but in reality will do harm.
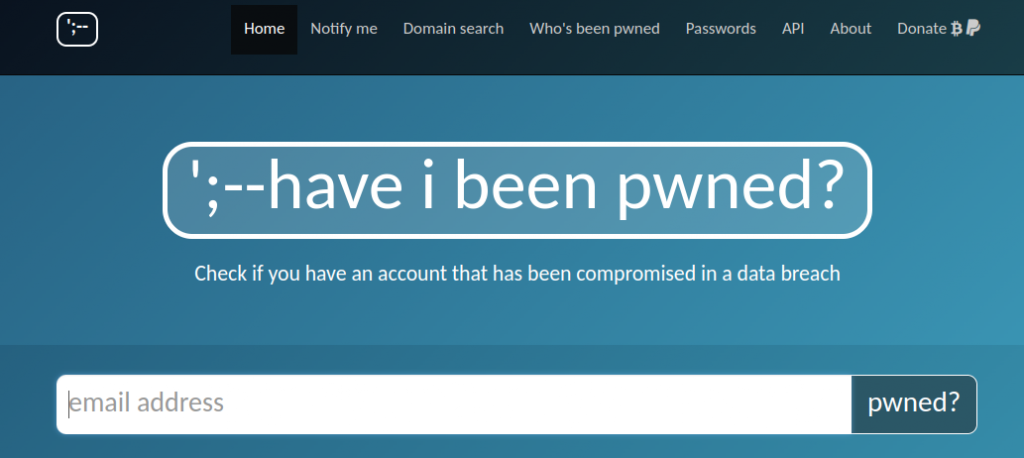
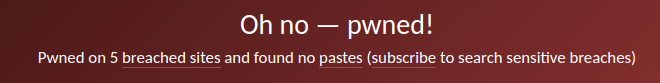
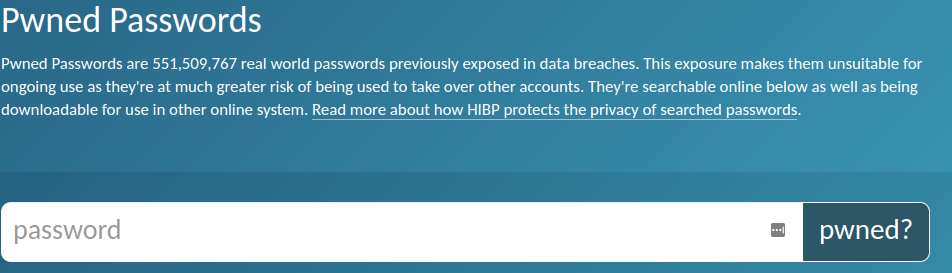
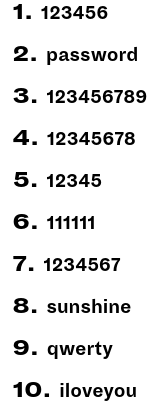
It’s also a good idea to take a fresh look at your password security. Turkish researcher Ata Hakcil analysed more than 742m passwords that have been revealed in data breaches (hacks) that turned up on the Dark Web. Ata went on to make a worrying number of discoveries.
Of the 742m only 169m were unique which just goes to show how frequently we reuse passwords and how many passwords are used by a lot of people.
Worst passwords of 2020
Unfortunately, not a lot has changed over previous lists
1/ 123456 (same place as 2018 & 2019)
2/ 123456789 (up 1 place) (same as 2019)
3/ passwords (up one place on 2019)
4/ qwerty (a fall of one place on 2019)
5/ password (slips two places)
6/ 12345678 (up 1 on 2019)
7/ 123123 (a new entry)
8/ 111111 (up from No. 10 in 2019)
9/ 1234 (yes, I kid you not, 1234)
10/ 1234567890 (a new entry in this Top 10)
Disturbingly, at least 1 in 10 people have used at least one of these poor passwords – I hope you’re not one of them.
Data breaches are inevitable. To be as secure as possible you need to use strong, unique passwords for each individual account that you have. This makes the theft of one password much less of a disaster than if you use the same (or close variant) across all of your accounts.
What’s a Strong Password?
A strong password isn’t a word at all. The best ones are passphrases comprising of a random combination of words with 12 characters or more, using mixtures of alphanumeric, UPPER & lower case characters and symbols.
Think of a nonsense phrase, or even a line from your favourite song. Science Friction Burns My Fingers for example. Noe, run the words together, use hyphens, underscores and number substitution.
Sc13nce-fricti0nBurnsMy_Finger5%
That’s one password – you need a unique one for EVERY account that you have. Now, that’s a challenge to remember so you need a password manager. Because of my work, I have access to 789 accounts of one sort or another and I have 789 different passwords. Obvious there’s no way I could remember all of those – I struggle to remember 4 important ones which his why I use a password manager. Not only does it store all of my passwords in a safe place it also generates new, random, ones for me.
Top 10 Password Managers
There are loads of great password managers out there. I use LastPass because it was one of the first to integrate with my browser AND be available across all of my devices, desktop, laptop, Chromebook, phone and tablet.
TechRadar recently reviewed Password managers and their top 10 free and paid-for password managers is as follows
1/ Dashlane
2/ NordPass
3/ RoboForm
4/ 1Password
5/ LastPass
6/ Keeper
7/ BitWarden
8/ LogMeOnce
9/ mSecure
10/ ZohoVault
You can read TechRadar’s reviews here. And don’t forget, your web browser probably has a password manager built in and may even generate new ones for you but it may not synchronise across all of your devices
And PLEASE, if this applies to to you – STOP USING PASSWORD or 12345678 and use one of the above instead
Have a great Christmas, a happy new year and I look forward to communicating with you in the new year. If you need any help, please, just ask. You can reach me by phone – 01793 238020 – email – andy@enterprise-oms.co.uk or just hunt me down on Social Media.