One thing that you can be sure of, when it comes to the world of SEO, is that 2024 will be different to 2023 and 2023 was different to 2022. And that’s just down to the way that Google, Bing, Yahoo etc work. They are all looking at the ways we use Search Engines and changing things up to make sure that they deliver the websites we are looking for.
So, without further ado, here are the Top 10 things you should be paying attention to to give your SEO a boost in 2024.
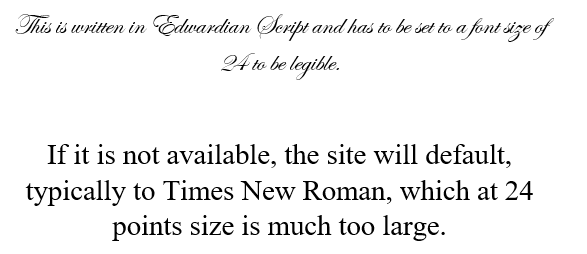
- Understand Core Web Vitals: Google’s Core Web Vitals are a set of metrics that measure the user experience of a website. These metrics include loading speed, interactivity, and visual stability. If your website doesn’t open quickly (in under 3 seconds) and people can’t understand what you do almost instantly, then your website won’t be generating many leads and opportunities.
2. Optimize for Google Passage Ranking: To think that Google only looks at web pages is so 2022.
Google’s Passage Ranking algorithm is designed to identify and rank individual passages of text within a web page. Google will look at the paragraphs and individual sentences on a page and will rank a page based on a single line, or paragraph, if it thinks that content is relevant.
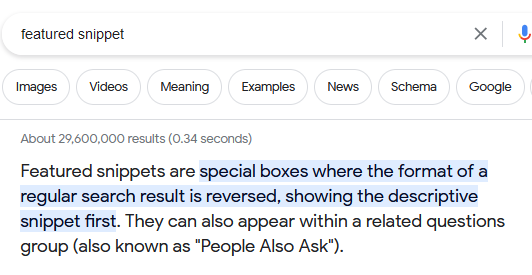
3. Focus on Featured Snippets: Featured snippets are the highlighted search results that appear at the top of Google’s search engine results page (SERP). Google can (and does) display parts of a web page if they answer specific queries in Google Search.
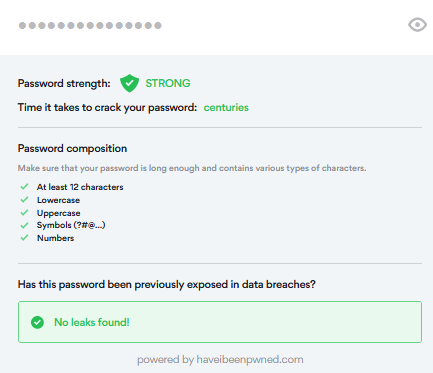
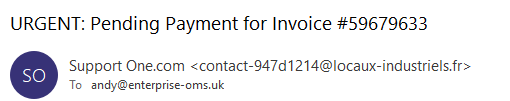
4. Learn the E-E-A-T Principle: E-E-A-T stands for Expertise, Experience, Authoritativeness, and Trustworthiness. To support your website, and help Google understand your business and how good your business is, you need to demonstrate your E.E.A.T in your content.
If you demonstrate E.E.A.T and your website becomes an authoritative go-to source for a topic (an individual content creator or a website) this demonstrates a very high level of E-E-A-T. For example, a content creator with years’ of first-hand experience in a topic where this is more important than formal expertise demonstrates a very high level of E-E-A-T.
5. Support Multiple Long-Tail Keyword Phrases: Long-tail keywords are longer and more specific keyword phrases that users are more likely to search for. Although using Long Tail Keywords won’t be as exciting as working on really popular keywords/phrases there will be much less competition which makes it easier to rank for them, ultimately leading to more visits to your website.
As an example, “SEO” is a high focus, popular keyword with millions of results which makes it extremely competitive and very hard to get a Page 1 placement for. However, “SEO specialist in Wiltshire” has much less competition, making it easier to rank for. It also means that people searching for an SEO specialist in Wiltshire who find, and visit, a website that meets their search criteria will be a far warmer lead.
6. Create New Content: How does a Search Engine tell that you are still in business? By regularly posting high quality content, that’s how. Not only that but you can focus your new content on specific issues to support your E.E.A.T. AND to focus on particular areas that need SEO support. Just make sure that it’s informative and relevant to your target audience.
7. Update Old Content: Updating old content is just as important as creating new content. Revisit existing content and bring it up to date to maintain its relevance for your target audience.
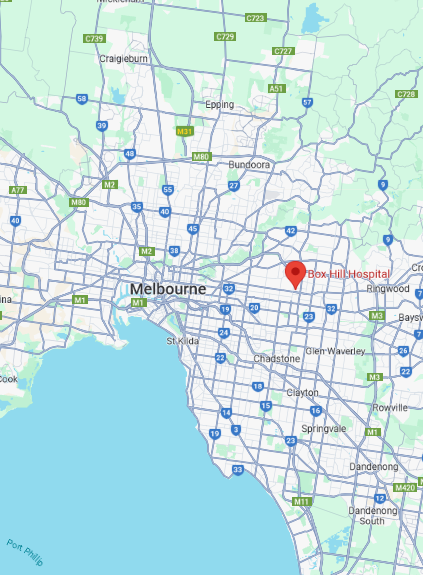
8. Understand the Importance of Local SEO: If your target market is local to your business then you need to focus on Local SEO. This will help Google understand Where you work so that people in your target area can easily find your business. Your free Google Business Profile (FKA Google My Business) is a powerful way to communicate the areas you cover.
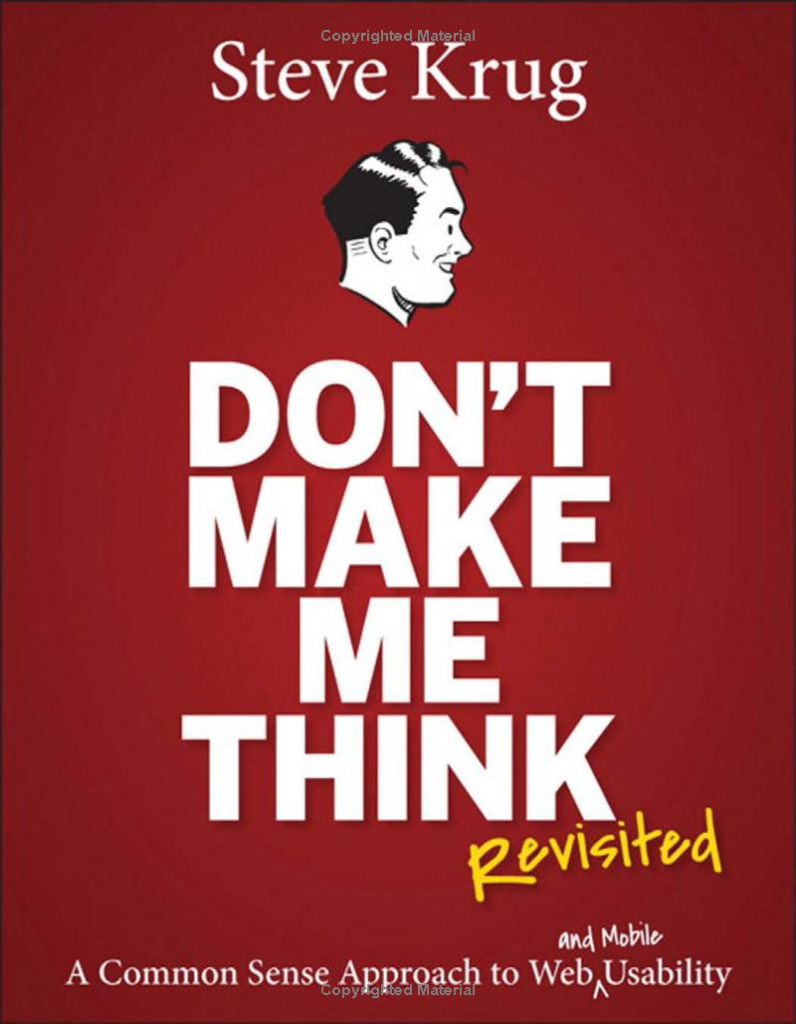
9. Focus on User Experience (UX) Optimization: Understand HOW people are navigating through your website and how people are actually using your website. This is called User Experience (UX) and optimising UX is a surefire way of keeping your audience engaged and encourages the actions that you want visitors to take. Contact, Subscribe, Download, Buy etc. And keeping visitors on your website for more time also supports your SEO because Google knows whether people love, or gate, your site.
10. Zero-Click Searches Take Over Popularity: A Zero-click search is any result that answers your question without you having to actually click to visit a website. (See Featured Snippets as an Example) It is expected that zero-click searches will become even more popular so you should take this trend in to account when designing, or redesigning your website.
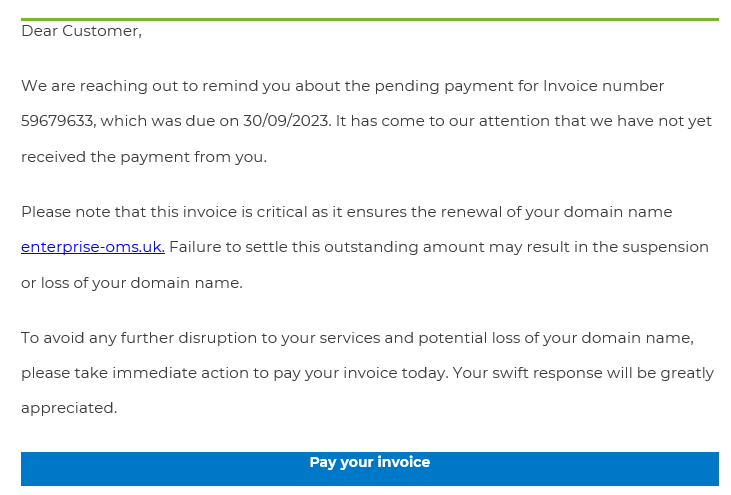
I hope this list is helpful and if you need help with your SEO then please, don’t hesitate to get in touch. Call me on 01793 238020, email andy@enterprise-oms.co.uk or just search Chief SEO Officer for a free chat about your business, your website and your SEO.