There’s increasing talk in the media, and in advertising, of VPNs as an apparent cure to all your security woes and as a potential money saver. But what is a VPN and do you actually need one?
What is a VPN and how does it Work?
The acronym VPN stands for Virtual Private Network. Virtual in that it’s not, in the strictest sense, real, your VPN only exists for the duration of your use, Private because your connection is encrypted which prevents bad actors form listening in and Network because your VPN builds a private network between your device and an endpoint. It’s often likened to building your own tunnel from you to the endpoint with the data being very secure as it travels through your own tunnel.
Do you remember in some old films when the detectives would say “we can’t track this person, they’ve bounced their call, internet connection etc, off at least 9 different servers across the world”? Well, they could have been using a VPN.
Back in the days when I was employed as a consultant, my employer used a VPN so that we could securely connect to the office network when working remotely. And that’s what a VPN does, it allows a more secure connection across the internet.
Your VPN provider has a number of endpoints that they provide, around the world and when you connect to one, your data is encrypted before it leaves your device and pops out on to the internet at one of these points-of-presence with everything in-between making it’s way through your own, encrypted, secure, tunnel.

Imagine you pop in to your local coffee shop and hop on their free wi-fi to check your emails, perhaps do a little shopping and check your bank account. All your data flows through your coffee shop’s wi-fi router (Local Network in the graphic above) and out on to the internet (Public Network). However, it’s very easy for someone with a malicious intent to set up their own connection to the cafe’s WiFi and pretend to be the free WiFi service. If you connect to this all your data goes through their system (and it could just be their laptop) which allows them to pick up your connection, analyse your traffic and steal your data. This is called a man-in-the-middle attack and is pretty common and very easy to pull off.
If you use a VPN it doesn’t matter about the man-in-the-middle because your data zips right past that, secure in it’s own encrypted, tunnel, on the way to the endpoint – which is where it gets decrypted and sent on it’s way to your chosen website.
Why Should I use a VPN?
There are a number of reasons why you might choose to use a VPN.
The first is SECURITY
As noted just now, it’s not overly difficult to intercept web traffic, some of which will contain personal data and security related info – user names, passwords, banking data etc and a VPN can overcome most of the risks associated with the interception of privacy related data, keeping you safe from identity fraud and theft.
The second is SAVING MONEY
Your VPN provider will have endpoints in a number of different countries and if you select one of those countries then the internet will think that’s where you are – because that’s where your internet connection and data look as though it’s originating.
This means that you might find subscriptions (Netflix, YouTube, Spotify etc) are less expensive in other countries, that flights and holidays may cost less if booked from somewhere other than the UK and so on.
For example,
It’ll take a little bit of research but here are a couple of examples.
- Spotify Premium costs just $1.58/month in India (the cheapest) but $18.39/month in Denmark (the most expensive).
- YouTube Premium is similarly priced, costing just $1.56/month in India but $15.95 in Switzerland.
Not all VPNs provide access to the least expensive countries but there are many good deals to be had, although you do need a VPN that is able to bypass Geo-Blocks, the technology that subscription providers use to catch VPN users and stop them getting the best deals.
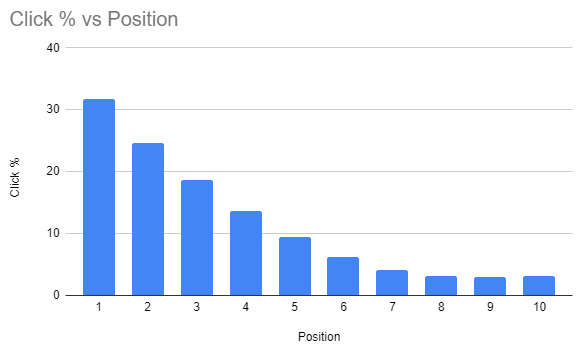
The third is HIDING YOUR LOCATION
When conducting an SEO review I have to appear as a random, anonymous, user when researching client sites. Unfortunately, due to the way that Google works, if I just use my regular browser, Google knows it’s me – even if I choose “Incognito” mode. This means that Google presents search results based on known likes, browser and search history and a wide range of other metrics – which is pretty useless.
So, I use a Browser that rejects cookies, stores no history and has a built in VPN. This ensures that I see results that are unfiltered, for the most accurate results. The Browser that I use for this is the Epic Privacy Browser and it’s free to download and use
I also have international clients and conducting a web search in the UK will show me results biased towards the UK. Again, by setting my VPN endpoint in the country I want to research it looks as though I am connected to that country and so I get to see search results from that country.
Some UK services, BBC iPlayer for example, block you from accessing shows and films when you are outside of the UK because they don’t have the necessary Copyright licenses to broadcast shows to the rest of the world. When on holiday abroad this could limit your access to entertainment. Using a VPN will help bypass this restriction.
Privacy
Many service providers on the internet use details from your internet connection to tailor services to you and target ads at you. A VPN will prevent them from attributing your browsing history to your PC/Phone although if you are logged in to Google, Facebook etc this becomes null and void.
A good VPN will also scan files as you download them, provide Ad Free results and ensure that there’s no data tracking or storing when you are searching.
So which VPN should I choose
As with all things technology related, the real answer is “it depends”. If you just want to anonymise your web browsing then browsers such as Brave (no VPN but blocks trackers and a lot of Ads) or Epic (the one with the inbuilt VPN – although it only has EndPoints in 8 countries) will be sufficient for your needs.

Probably the most well known VPN is provided by Nord and they regularly run a range of special offers. Their normal price is £94.35PA for a 2 year contract although this does enable you to use their VPN on up to 6 different devices. However, at the time of writing this is reduced to £33.65PA or just £2.49/month and you get an additional 3 months free (prices are exc. VAT)

Another leading VPN is SurfShark. Their “Unlimited VPN” package is currently just £1.74/month for the first 26 months and can be used on an unlimited number of devices

My current VPN of choice is TunnelBear but for no other reason than when I signed up I got a lot of bandwidth for very little money. It has some limitations but none that I have found impact on my use

If you have a 2TB plan (or greater) storage plan with Google then you can use their free “1” VPN on phones (Android and iOS). However, it does mean that you are trusting Google not to look at your data as it passes through their servers. You also can’t control your EndPoint so it’s no good if you want to browser from different countries
VPN Drawbacks
- Beware of “Free” VPNs because nothing’s ever free. A free VPN may come with ads and it might also sell your data on to unidentified third parties.
- Free VPNs also may limit the Bandwidth they provide which will limit the downloads and streaming you can do.
- Free VPNs may also limit your Speed which also makes them useless for streaming and downloads will take quite a while longer than you are probably used to.
And finally, if you have any VPN related questions then I probably know enough to be able to answer your question or point you in the direction of someone who can.
If you need assistance with your SEO, Email Marketing, Social media or any other type of online marketing activities then I can definitely help you so you really should get in touch – even if it’s just for a free consult. You can call me on 01793 238020 or 07966 547146, email andy@enterprise-oms.co.uk or book a slot using my calendar and we’ll take it from there