With the news that 30m credit and debit card details from US customers and over 1m sets of card details belonging to visitors to the US, have been put up for sale on the Dark Web following a malware attack against US convenience retailer Wawa I thought I’d take time out to explain why small businesses are just as at-risk from hacking as large organisations.
With the news that 30m credit and debit card details from US customers and over 1m sets of card details belonging to visitors to the US, have been put up for sale on the Dark Web following a malware attack against US convenience retailer Wawa I thought I’d take time out to explain why small businesses are just as at-risk from hacking as large organisations.
But first, let’s take a look of some of the major security breaches that occurred last year. According to Risk Based Security’s Data Breach Report there were 5,183 breaches by the end of September 2019 alone. These exposed more than 7.9 billion records. This was a 33.3% increase on the same period in 2018.
Here are some of the worst breaches.
- Orvibo Smart home products – 2 billion records discovered on an unprotected database. These comprised of private individuals, hotels and businesses who were using Orvibo’s smart home devices. The data included email addresses, passwords, user names, family names and addresses.
- Dream Market Breach – 617m online account details stolen from 16 hacked websites, including MyFitnessPal (151m). Data stolen included user names, passwords and email addresses.
- Canva – 139m records stolen, names, user names, passwords, email addresses and location.
- Capital One – 106m records hacked with names, addresses, credit scores, email addresses, dates of birth and more stolen.
- Words with Friends – 218m records stolen, including names, email addresses, passwords, phone numbers and, where linked, Facebook ID info
However, these are just some of the ones that hit the headlines. Thousands don’t, particularly attacks on smaller businesses. Research indicates that nearly 70% of SME’s experience cyber attacks (Ponemon State of SMB Cyber Security 2018) but why SMEs?
I talk to many people who believe their businesses are too small to have anything of value to the hackers. However, the truth is that they are too small to have a dedicated cyber security officer/specialist and so are easy targets.
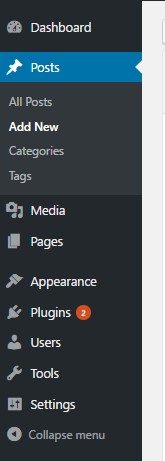
 Let’s take websites – most businesses use WordPress – over 1/3rd of websites use it. There’s nothing wrong with WordPress but, as the world’s most popular web development tool, it is also the hackers main target. (A bit like the way Windows is targeted compared to Apple’s operating system – its all in the number of targets)
Let’s take websites – most businesses use WordPress – over 1/3rd of websites use it. There’s nothing wrong with WordPress but, as the world’s most popular web development tool, it is also the hackers main target. (A bit like the way Windows is targeted compared to Apple’s operating system – its all in the number of targets)
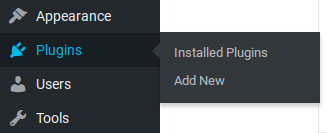
WordPress is pretty secure and there are Plugins to make it more so BUT you have to keep everything up to date. Keep WordPress up to date, keep your plugins updated too because if you don’t you might be leaving holes in your security for the bad guys to exploit.
But why would they?
- Small companies are frequently connected to larger organisations and they might be a way in
- Hacked systems can store illegal material
- Hacked systems can be used in attacks on other websites (DDoS)
- Hacked systems can host Malware
- Hacked systems could provide access to valuable Intellectual Property
- Hacked systems could provide easy access to other valuable data
Malware
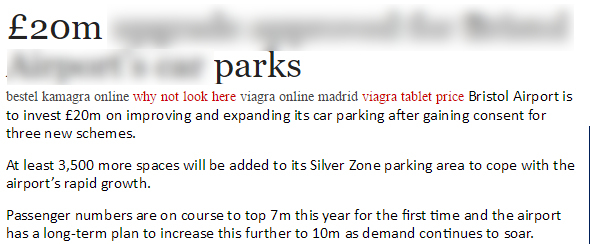
 Imagine you have a reasonably popular website. Hackers will look to gain access to your site and plant malware on it that will automatically download (and install) itself on the computers of everyone who visits your website. The malware could allow the hackers to record the keystrokes of infected machines, could enable the hackers to take remote control of infected machines or turn them in to storage depots for illegal material.
Imagine you have a reasonably popular website. Hackers will look to gain access to your site and plant malware on it that will automatically download (and install) itself on the computers of everyone who visits your website. The malware could allow the hackers to record the keystrokes of infected machines, could enable the hackers to take remote control of infected machines or turn them in to storage depots for illegal material.
Imagine how your reputation will suffer when this comes to light.
- Keystroke recorders
A keystroke recorder does what it says on the tin, it records every single keystroke made on a keyboard and secretly transmits it to a malicious 3rd party. This could be bank/card details, online shopping details, log-in user names and passwords, and much more - Remote Control – DDoS (Distributed Denial of Service Attack)
With the ability to remotely control your PC, and hundreds or thousands of others, malicious 3rd parties can “take down” target websites simply by overwhelming them with more web traffic than the website can cope with. Remember what happens to the Glastonbury website when the tickets are released – although not malicious the number of people desperate to get their tickets tend to bring the website to its knees as soon as tickets are made available
Imagine a bookmakers website going off line a week before a major betting event. They’d be contacted by the Cyber Criminals who will admit responsibility. The bookmakers will then be told to “pay up” or their website will be blocked again, much closer to “big day” and prevent bets being placed. - Illegal data storage
Imagine the scene. There you are working in your office and there’s a battering ram through the door followed by police storming in with a warrant to take ALL of your computing devices. Your business will grind to a halt but why have you been targeted? Simples, as the meerkats say – the police have identified one or more of your computers/servers as the source of illegal material. This could be pirated software, music, films or worse. In the worst case scenario this information hits the local (and possibly national media) and your reputation is trashed. And you may not even have been at fault! - GDPR
Under all of the above scenarios you’ll probably have to report the matter to the Office of the Information Commissioner (ICO) under GDPR. After investigation, If your security and procedures are found wanting then you might be liable for a fine. GDPR states that fines can be up to 4% of your turnover, and that’s no laughing matter
How do I prevent this happening to me
No security system is 100% watertight, there are just too many variables and access points. The closer you get to 100% the more expensive it becomes to close those last few security percentage points. However, like home security, your job is to make sure that your security is as good as it can be so that the bad guys choose an easier target.
Get in touch with a good IT company or Cyber Security company or you could #AskAndy. Drop me an email – andy@enterprise-oms.co.uk or give me a call on 01793 238020 and we can start the ball rolling. I know that I’m not a security consultant but I know quite a bit and can always point you in the direction of a trusted third party if you need more help.